What Is a Network Security Key? Understanding a Crucial Digital Security Concept


The evolution of the internet and technology has been swift. Online users have more access to tools and digital services than ever before, providing them a previously unimagined level of information and convenience.
However, alongside the rapid development of the internet has been a growing number of cyber threats. From individuals having their credit card numbers stolen to massive corporate data breaches, the threats to online security are real, but tools are in place to keep these attacks at bay. Network security keys are digital measures that help to protect internet users when they’re online.
Dive into how network security keys help to keep internet users and their information safe and protected.
Definition and Purpose of Network Security Keys
What is a network security key? Essentially, it is the password or code needed to access a local area network. Most of us are familiar with network security keys ― at home, you use one to join your personal Wi-Fi network. Network security keys allow users to establish a secure connection and prevent unauthorized access to the network.
For example, diners who wish to visit a website using a restaurant’s local network would likely have to connect using the security key of that particular network. This may include entering a specific password to access the key, which the users’ devices can remember each time they try to log in to that network.
Users who connect to an airport’s Wi-Fi network may have to pay a fee and input personal information. That information is protected thanks to the security protocols in place in the network itself. Those who don’t have the necessary key or password would have difficulty trying to compromise or attack a network user’s information. Breaches do still happen, but these keys reduce the probability of criminal incidents.
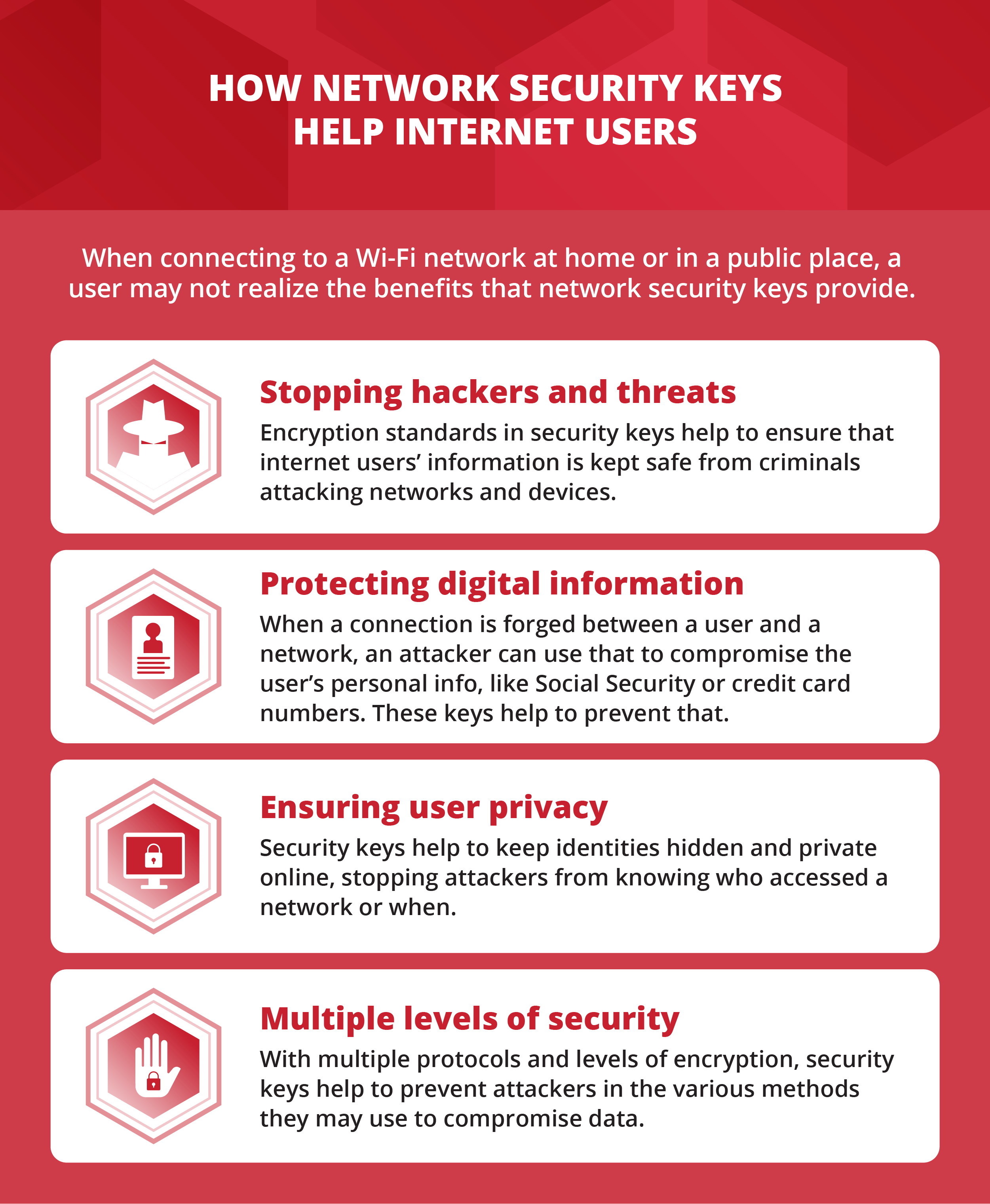
Benefits of Network Security Keys: Protection from a Range of Cyber threats
The primary benefit of network security keys is ensuring that digital users’ information is safe. Secure wireless networks help prevent a variety of different types of online threats, according to the U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA). Here are some examples:
Piggybacking
Piggybacking occurs when a user connects to an unprotected or a poorly protected wireless network in close range, such as a neighbor’s Wi-Fi network. That neighbor could have the ability to access and compromise the initial user’s information, or potentially attack the network itself. Because people rarely monitor who’s logged on to their network, they may not be aware that piggybacking is taking place.
Wardriving
Wardriving is a more targeted version of piggybacking in which hackers single out unprotected or poorly protected Wi-Fi networks in close range. According to CISA, this can include someone driving down the street, connecting to a network, and compromising the information of other connected individuals.
Evil Twin Attack
An evil twin attack entails a false network that closely resembles a legitimate one — for example, a Wi-Fi network similar to that of a coffee shop’s, which appears to have the same security protocols and that dupes users into believing that they have connected to the coffee shop’s actual network. Those users could then easily have their data compromised.
Wireless Sniffing and Unauthorized Computer Access
Wireless sniffing and unauthorized computer access occur when individuals seek out poorly or unprotected networks and are able to access and compromise sensitive data communicated through and within them, such as credit card numbers provided for online transactions or personal files on a digital device. Often, because people aren’t actively monitoring who’s connected to a network, they’re unaware that these activities are taking place.
Shoulder Surfing
Shoulder surfing is less sophisticated than other digital risks but just as dangerous. It occurs when an individual observes the information another user is inputting into a computer or mobile device. For the user at a coffee shop, a shoulder surfer could figure out a network password or personal information, such as a Social Security number or home address, simply by watching the information typed into the device.
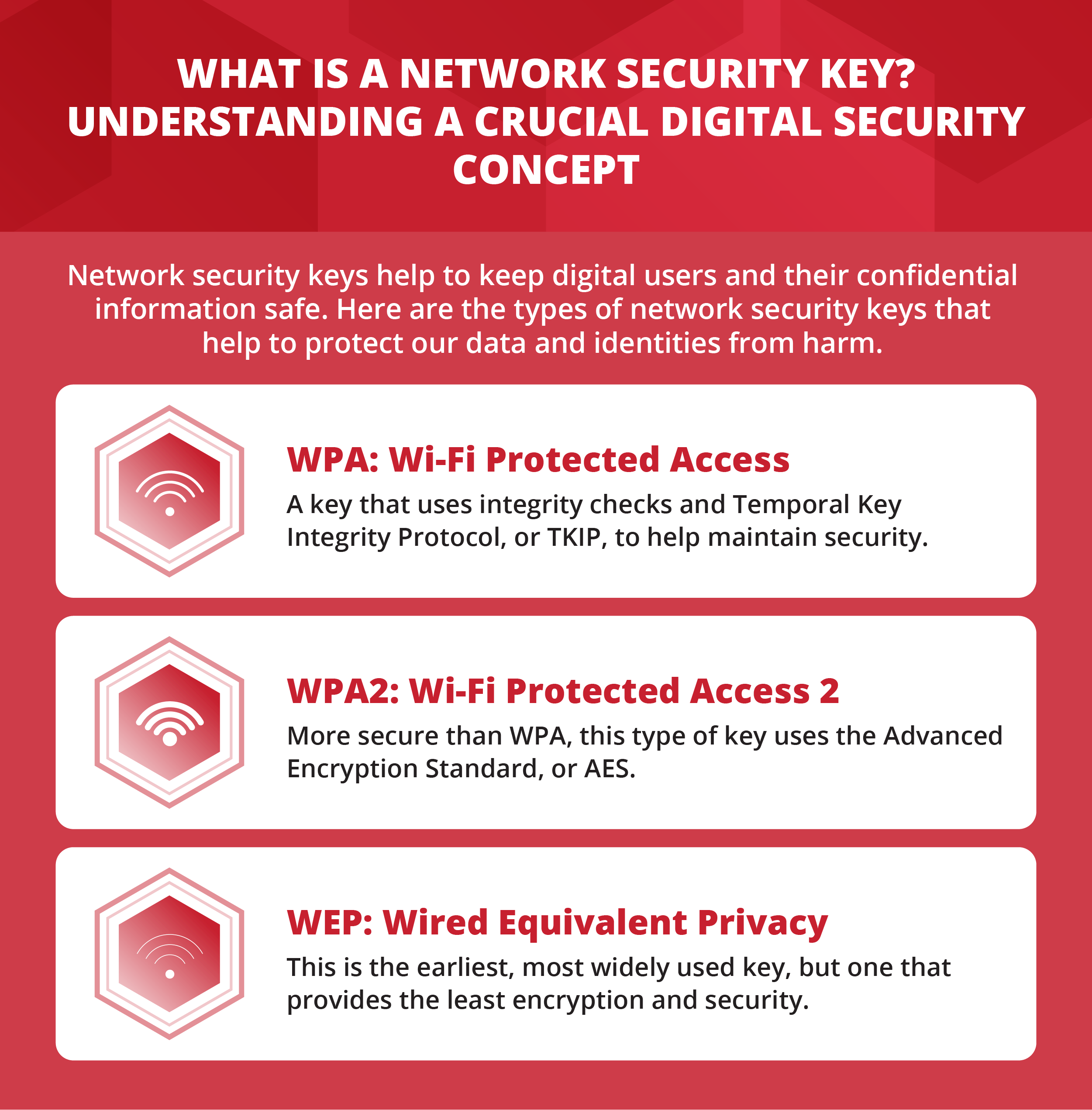
What Are Types of Network Security Keys?
There are different primary types of security keys, each with unique benefits.
WEP
According to Ars Technica, “[W]hen the original 802.11 Wi-Fi standard released in 1997, it included WEP — Wired Equivalent Privacy — which supposedly offered the same expectations of confidentiality that users today now expect from wired networks.”This type of key uses hexadecimals, which are 10- or 26-digit keys containing numbers (from 0 to 9) and letters (from A to F), for example, 0FAB571CD5. “Later revisions of WEP offered the ability to automatically hash a human-readable password of arbitrary length into those 10- or 26-digit hexadecimal codes in a way that was consistent between the clients and the routers,” according to Ars Technica.While common, WEP keys show vulnerabilities in their encryption and security protocols. With WEP keys, the same encrypted message is provided in every connection, meaning that everyone with access to the same key on a given network has access to each other’s information. Research from Kaspersky notes that WEP keys are still commonly used in some parts of the world.
WPA/WPA2/WPA3
Wi-Fi Protected Access (WPA) keys are seen as an upgrade over WEP due to their ability to accept human passwords and conceal a user’s information from others on the same network, as well as authentication codes that make information sent across networks more secure. “Connecting to a ‘public private’ Wi-Fi network where everybody knows the password no longer meant sharing everything you sent and received with anybody else who happened to be nearby and know the password,” according to Ars Technica.Just as WPA keys are an upgrade over WEP keys, WPA2 keys provide network users even more security. According to Lifewire, “WPA2 further improves the security of a network because it requires using a stronger encryption method called AES,” or Advanced Encryption Standard. AES works by using block ciphers to encrypt and decrypt data, TechTarget reports.
WPA3 keys go even further in their authentication protocols. Writing in a post for InformationWeek’s Dark Reading, Curtis Franklin Jr. states that “the primary enhancement to WPA3 Personal is in the authentication process, where WPA3 makes brute-force dictionary attacks much more difficult and time-consuming for an attacker.”
However, just because WPA, WPA2, and WPA3 keys are all improvements over their predecessors, they don’t fully ensure security on a given network. Hackers can still compromise or access keys with enough effort and ingenuity. Even users connected to more secure networks can find themselves exchanging information with others on less secure ones, which can compromise their own security and data. Users should always practice caution when sharing sensitive information on any connected network.
Two-Factor and Biometric Keys
Biometric and Two-Factor keys are similar to WPA and WEP keys in that they work to provide security to users accessing a given network, but are different in that they require some sort of external or two-factor authentication. For example, Yubico provides hardware authenticator tools that can help ensure that a person connecting to a network or a device is who they say they are. Users can insert YubiKeys into a PC, and are then prompted to press their key for authentication before being given network access. The additional “physical” or external layer of this kind of two-factor security protocol helps to ensure the network and its connected devices are protected.
Other biometric security features include fingerprint scanning and facial recognition. By providing some sort of physical or human identifier, they help to ensure that networks remain secure. Still, even with these enhanced features, security can be compromised. A person who accesses a network using two-factor authentication may still fall for a phishing scam, giving out private and confidential information to someone posing as a legitimate company or organization.
Similarly, a person who accesses a network using two-factor authentication or biometric options may inadvertently download malware or other harmful software that can then compromise their information and larger network security. While two-factor authentication and biometric options help to keep networks secure, users on those networks should still be aware of the information they’re sharing.
What Do Network Security Keys Protect?
It’s important to understand exactly what network security keys help to protect.
Keep Networks Safe from Hackers
Hackers and cybercriminals can have various intentions when attacking a network. They may want to expose a corporation’s sensitive data and information. They may want to cripple the network itself to stop a person or an organization from accessing the internet. They may also want to simply play pranks. Whatever the intent, security keys work to thwart hackers and criminals.
Protect Users’ Identities and Information
When people access a network, they often exchange more than just usernames and passwords. On a poorly protected or unprotected network, information regarding people’s identities, including addresses, financial information, employment details, and other sensitive data can be compromised. On a secure network, keys, protocols, and encryption standards help to keep that information private.
Keep Valuable Software and Hardware from Becoming Compromised
In 2014, Sony Pictures Entertainment was hacked by a group that not only stole massive amounts of sensitive data, but also temporarily made individual users’ devices unusable. Additionally, individuals connected to poorly protected or unprotected networks may inadvertently download malicious spyware or malware that can harm their devices.
How to Find a Network Security Key
Network security keys help to ensure that users and their data are kept safe and secure. There are different ways to find network security keys on computers and mobile devices.
Desktop
Lifewire provides a thorough, easy-to-understand explanation of how to locate a network security key on a personal computer. Users can access their particular routers as administrators, then find information regarding the network ID and passkey, as well as identifying connected devices. For users, this can be helpful to find out if the router or network has been compromised and if users are connected to it without permission. The administrator can then take measures such as changing the network password to improve security.
Mobile
Some smartphones can act as personal hotspots to access the internet and generate their own network security keys. On an iPhone, this security key can be found by accessing the iCloud settings, then enabling the Keychain feature, according to Lifewire.
From there, a user can enable a personal hotspot; connect with a Mac computer; launch Keychain Access; and then locate the service set identifier (SSID), which acts as the name of that network. Then, they can click to show the password for the network, which, if administrator privileges have been granted, reveals the key. On Android, a security key can be found using a file manager app. Individuals can also change the password in the hot spot app on both iPhone and other devices.
Network security keys are often the first line of defense against cyber attacks. Understanding how they work, and the importance of having a strong passcode, can help users and their organizations keep their valuable data safe.
Additional Sources:
Avalan Networks, “Advantages of Network Security”
Techopedia, “Network Security Key”

